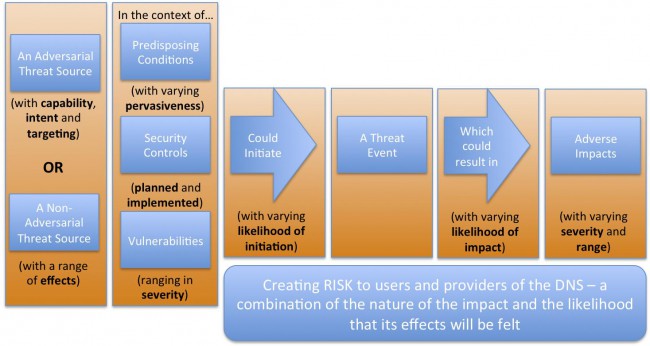
I’ve been spending a fair amount of time working on an ICANN cross-constituency working group that’s taking a look at the risks to the DNS. Our gang just posted a major report today and I thought I’d splash this up here so I can brag about our work on Twitter and Facebook.
Category Archives: Policy & regulation
Mikey in the high branches.
This is a post that most readers of this blog are going to scratch their heads over. I volunteered a fair amount of my time to ICANN (the organization that works on the domain-name and numbering systems that underpin the Internet). Until yesterday. I got pretty cranky over an email exchange that I (as a working-group member at the bottom of ICANN’s bottom-up policy-making process) had with a couple Big Kids on the Council that manages our working-group-based policy-making process. I loudly resigned over this — here’s a link to my grouchy email to the community. Continue reading
Whit Diffie is the new VP of info-security and cryptography at ICANN! Kewl!
Very neat news today out of ICANN. Whit Diffie is this monster figure in the crypto world — he’s one of the founding folks in that circle. He worked at Sun for ages and now he’s joining ICANN.
Click HERE for the ICANN press-release.
Click HERE for a starter-page at Wikipedia.
Click HERE to watch him on an episode of Cranky Geeks (with John Dvorak) to get a feel for what’s he’s like in person.
I’m really glad to hear that he’s joining the ICANN gang. It’ll give us some depth that we badly need in this area.
Remembering why I voted Obama…
Here are links to his first State of the Union speech and the Q&A portion of his remarks to the House Republicans two days later. The real deal instead of the sound bites. Hey, this guy’s still got it for me. Just sayin’…
State of the Union
Q&A – Republican Caucus
Muni WiFi — let’s build a model
I just posted a story over at the St Paul Broadband Committee site about my belief that a lot of the municipal WiFi networks don’t seem to be grounded in financial reality.
Here’s a link to the article and here’s a link to the muni-WiFi financial model I built to go with it.
Here’s the deal — let’s get these models out of the hands of the VooDoo consulting expert type people and into the hands of the people. “Open source financial modeling” if you will. Let’s beat on this model — or write a new one if this one is hopeless — and get to the point where we ALL understand the economics that underpin these projects.
That way, we can either rejoice in bridging the digital divide, solving the problems of the world and putting a chicken in every pot (as advocates claim) or we can avoid the mess that comes with yet another technology project that over-promises and under-delivers.
What say you? Let’s have at it.
Good words for Qwest
I’ve been grouchy about Qwest in the past, sometimes even way beyond grouchy into the “troublemaker” category.
But today it was reported that they are the only RBOC holdout in the NSA’s program to build a database of every dang call made in the USA.
Kudos to Qwest for holding those call records back. Stick to your guns, folks.
Corp.com registry
The latest project to keep me away from this blog is bringing up the registry for CORP.COM domain names.
This is a project that Edmon Chung and I started back in 2002 when Edmon was the hotrod young entepreneur in charge of Neteka. He did such a great job that they got acquired by Afilias not long after we started our project.
What with Edmon distracted by the acquisition, and me distracted with a series of really interesting InstantCxO engagements, the Corp.com Registry sorta went on the back burner for a few years. But the time seemed right to both of us last year and the project is galloping toward an April launch.
2nd level domains like CORP.COM have been steadily gaining favor over the last few years, which is another reason why it seems like the time might be right to kick things off. Afilias is game, Edmon is game, I’m game, we have our first registrar in NamesBeyond. So off we go.
Regulatory Issues — Speech
I'm off to give a speech to the assembled regional telecommunications lawyers gang this morning — my topic is the regulatory issues in VoIP. Good thing there are folks like Jeff Pulver out there doing a great job of blogging this issue — there's an amazing amount of stuff going on in this arena with new twists every day. Read his stuff to stay up to date.
Here's the outline of my speech.
How should we classify VoIP?
– A voice service?
– A mobile service?
– A data service?
Which way should we be consistent as regulators?
– By technology?
– By service?
– By layer?
Which things do we want to break?
– Universal Service?
– Access charges?
– Long-distance rates?
– LATAs?
– POTS?
– The Internet?
– CALEA?
– Numbering?
– Disability access?
– 911?
Whose ox do we want to gore?
– LECs and CLECs?
– LD Carriers?
– VoIP over Internet providers (eg. Vonage)?
– ISPs?
What is our goal?
– Promote new technology adoption and investment?
– Preserve existing investments/infrastructure?
– Assure quality and standardization?
– Level the playing field?
– Assure non-discrimination and access?
– Promote competition and lower prices?
Who does the regulating?
– International – ITU?
– National – FCC?
– State – PUC?
– City – Cable Commissions?
– Nobody?
Spoofing caller ID
Ooo, now this one’s interesting… Here’s a writup in The Register talking about how some clever folks have figured out how to fiddle with caller-ID strings in the VOIP world — in both directions (inbound and outbound). Here’s a link to the article.
Hardly a “harmless prank” this could have some pretty nasty implications for stalking and identity-theft reasons. Read on for a few thought-provoking quotes…
Quote:
Callers with life-or-death anonymity concerns might consider spoofing just to get a little privacy. For now, Lucky says pranks among friends are the most common use that he’s seen of VoIP spoofing, but he believes that identity thieves and other swindlers could have a field day. “I’ve used it myself to activate my own credit cards, because I never give credit card companies my real number,” he says. “One simple spoof, and it’s like saying, if you have the guy’s phone number, that piece of information is more important than his mother’s maiden name and date of birth. If you have the phone number, you don’t need anything else.”
How ’bout them apples? This could cause the financial-services crowd a fair amount of heartburn. But what about the implications for people who are tangled up with a stalker? Here’s another quote:
Quote:
Privacy advocates, who had reservations about Caller ID when it was introduced in the 90s, aren’t happy that it’s becoming easier to subvert. “A worse case scenario is if you have a blocked number, and you’re a victim of stalking, and you’re duped into calling a number the stalker set up that was routed through a VoIP line,” says Jordana Beebe of the San Diego-based Privacy Right’s Clearinghouse. “It could put their life in danger.”
I’m also really interested in the regulatory impacts of VOIP, and this promises to generate a lot of pain on that front as well. Once again, here’s what The Register has to say:
Quote:
This arrangement relies on telephone equipment at both ends of the call being trusted: the phone switch providing you with dial tone promises not to lie about your number to other switches, and the switch on the receiving end promises not to reveal your number if you’ve asked that it be blocked. In the U.S. that trust is backed by FCC regulations that dictate precisely how telephone carriers handle CPNs, Caller ID and blocking. Most subscribers have come to take Caller ID for granted, and some financial institutions even use Caller ID to authenticate customers over the phone.
Stay tuned, this will be coming up again. Fersure…
VOIP — topic introduction
Ralph Jenson and I built us a pretty-darn-close-to-perfect copy of Vonage back a couple years ago and were within a whisker of kicking it off here in the Twin Cities. Unfortunately, Vonage came to town a year earlier than we thought they would and blew us out of the water. But I've been tracking VOIP stuff ever since.
These days the most interesting thing to me is the regulatory rasslin' that's going to be going on, so this will mostly be policy-wonk stuff. Heck, I've got to give a speech about VOIP regulatory impacts in a few weeks. That research alone should fill up several good blog entries.