This is a scratchpad post to collect “stuff” for the upcoming 50th anniversary of WORT. Cautionary notes: the newsletters and other documents behind the “click here” links are hosted here on my site. Also — this is still under heavy editing/development (I’ll take this warning down when I feel like it’s close to done).
Category Archives: Technology
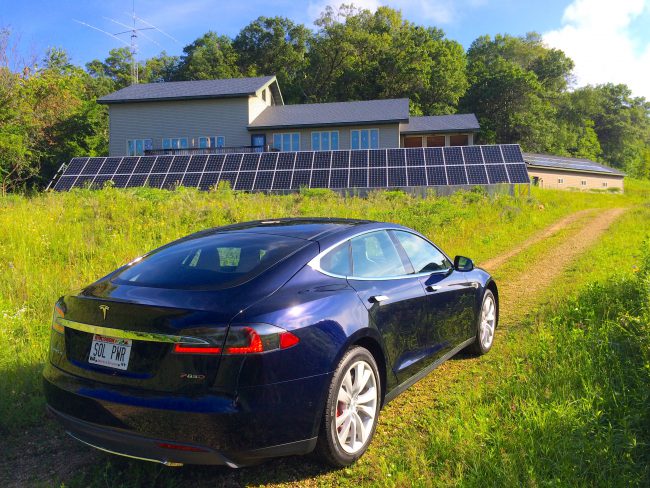
Talk: Restoring a Prairie Haven with renewable power
NEWS
July 1, 2016
For Immediate Release
Wings Over Alma welcomes Mike O’Connor to present:
Restoring a Prairie Haven with Renewable Power
Adding SSL to my OSX server
I decided it was time to make a little statement and add “always on” encryption to this completely innocuous site. The online equivalent of moving a lemonade stand inside a bank vault. Now when you read about refurbishing my car, or fixing a seed drill, you’ll be doing it over an encrypted connection.
This is another scratchpad post for folks who run an OXS Server and want to use a multi-domain UC (unified communications) SSL certificate. The rest of you can stop here — this is probably the most boring post of all time. Continue reading
Migrating from Snow Leopard Server to OSX Server (Mountain Lion)
Back in late 2011 I wrote this scratchpad post to document my efforts to move from Snow Leopard Server to Lion Server. I ran into some configuration problems that stumped the 2nd-level folks at Apple and eventually I abandoned the project and stayed on Snow Leopard.
When Mountain Lion came out, and went through an update or two to iron the kinks out, I decided to have another go at it. I’m crossing my fingers here, but I’ve been on OSX Server (the new/old name under Mountain Lion) for about a month now and things look pretty stable. So here’s another scratchpad post to document what I did to put back a few things that were removed from the standard OSX Server environment. Continue reading
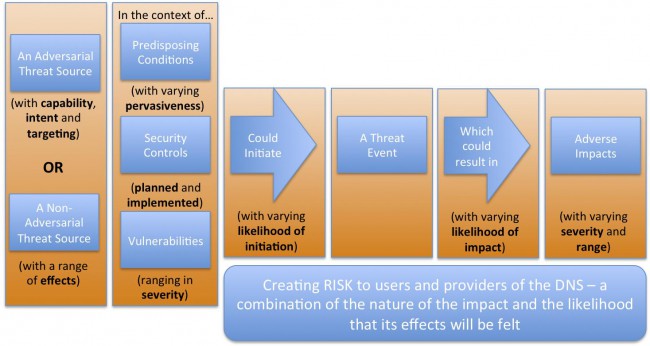
DSSA — DNS Security and Stability Analysis working group
I’ve been spending a fair amount of time working on an ICANN cross-constituency working group that’s taking a look at the risks to the DNS. Our gang just posted a major report today and I thought I’d splash this up here so I can brag about our work on Twitter and Facebook.
Grinnell Reunion 2012 — a life of happy accidents
I gave a talk at my Grinnell College reunion last weekend and decided to build this post to share a bunch of links to things that I talked about. This ain’t a’gonna make any sense to the rest of you. But the stuff is interesting. 🙂
This is a story of rivers of geeks. I described the rivers that I swam in during my career, but these are by no means all of the species of geeks that ultimately built the Internet. I was lucky to be a part of a gang of 10’s maybe 100’s of thousands of geeks that came together in the giant happy accident that resulted in this cool thing that we all use today. But don’t be confused — it was a complete accident, at least for me and probably for all of us. Here’s a diagram…
Adding capabilities to Mac OS X Lion Server
UPDATE:
I never converted to Lion Server. You can sortof see things unraveling in the middle of this post. I’m taking another run at it now that Mountain Lion Server (now renamed back to OSX Server) is getting stable. I sympathize with what Apple is trying to do. If you’re kindof the power user in the office, the newer version of Server is much better for you. But for those of us who were using the server to do slightly more complicated stuff, it’s been a long hard road.
I’ll write another post pretty soon that summarizes how I put stuff back into Mountain Lion Server. It’s still not easy, but it’s going better — at least so far. For now, just ignore the rest of this post. It’s out of date, and it didn’t result in a working server. Continue reading
Online privacy tips
A friend asked Marcie about reducing her exposure to ads on Facebook and I decided to write up the answer as a blog post so it would be easy to send to others (and update with new stuff). So here is a list of stuff that I do — your mileage may vary. I update this about once a year with new/improved plugins/tips. Continue reading
Fiber to the farm
Hooray! Our local phone company, good old Nelson Telephone Cooperative, is plowing fiber into our house at the farm over the next few weeks! You haven’t lived until you’ve seen me, an aging 60 year old geek, doing cartwheels in anticipation. So here’s a post to document the process as it unfolds.
Domain-names — Develop? Park? Sit tight?
Photographer: Gregory Szarkiewicz
I have a gaggle of terrific domain names (bar.com, pub.com, grill.com, etc.) that I’ve had Since The Beginning. Over the years I’ve pondered what to do with them and always come back to “sit tight” as my strategy. I saw a great article today that lays out the reasons why. Here’s the link:
http://www.domainnamenews.com/domain-development/mass-development-flawed-model/8058#more-8058
Whit Diffie is the new VP of info-security and cryptography at ICANN! Kewl!
Very neat news today out of ICANN. Whit Diffie is this monster figure in the crypto world — he’s one of the founding folks in that circle. He worked at Sun for ages and now he’s joining ICANN.
Click HERE for the ICANN press-release.
Click HERE for a starter-page at Wikipedia.
Click HERE to watch him on an episode of Cranky Geeks (with John Dvorak) to get a feel for what’s he’s like in person.
I’m really glad to hear that he’s joining the ICANN gang. It’ll give us some depth that we badly need in this area.
Why I returned my iPad after 3 hours
Actually the headline promises more than I can deliver. I don’t really know why I returned my iPad after 3 hours. I guess it just didn’t deliver $600+ worth of smiles. But here are a few things that contributed to the decision… Continue reading
How OK Go made their latest geek extravaganza
Complete geek heaven. Great band. Great Rube Goldberg device. 4 videos describing the collaboration they put together. Must see, if you’re a geek.
Consensus decision making — WORT-FM, 1975
This is a piece by Jeff Lange in Volume One, Number Three of “Spread the WORT” — the newsletter of WORT-FM (Madison, WI) just as it was going on the air in 1975. I’ve always loved this description of the consensus decision-making process we used to run the station. All due apologies to Pogo…
The big deal? The sentence that really catches it for me is “we ad WORT don wanna tred up on the wee miroridy vuponts, so we jus wade undill eberyone am finely agreed.” Still works for me today, some 35 years later. Thanks Jeff!

Here’s my translation, since many of you aren’t native-English speakers and might find this pretty tough to read in Jeff’s native Pogo-style language. Apologies to Jeff for any mistranslations.
Yes, it’s a curious fact, that nobody is ever able to quite explain, how decisions get made at this particular radio station. But they do. This is a grievous hard and ticklesum thing for newcomers to digest. Take, for example, the familiar caller who, in a fever pitch of excitement, has phoned up the station with his or her (or “it’s” for that matter) idea for a program. Rnnng. He (let’s just say it’s a “he”) says “My dog can bark heavy metal rock n’roll — can he have 5 hours on Tuesday nights?” Well, the person at the station (say it is a person) says “Isn’t that the same thing as what’s on WBRK every night?” The caller replies “Yes, but my dog barks badder!” Then that, says the person, is a question for the Program Committee.
The best thing then is if the caller hangs up, thinking all is well for the Program Committee will do its duty. But if the caller says “Oh, what’s the Program Committee?” then the person has to explain: The Program Committee are all the people that come to the Program Committee Meeting. You can come. So can your mother. It’s Friday at 8pm. No, they never vote on anything. Voting is against the rules. So is parliamentary procedure. They just talk about things until everyone is agreed, and that is consensus — the highest form of unanimity.
Then the caller says “oh.”
Then the person at the radio station should continue: “Yes, it’s a curious fact, but it seems to work. So far, at least. We at WORT don’t want to tread on the wee minority viewpoints, so we just wait until everyone is finally agreed. Nope, it’s never failed yet… which just goes to prove: you can make some of the decisions all of the time, and all of the decisions some of the time…”
Then the caller says, “can you put me through to the general manager?”
“No, there isn’t a general manager. Would you like to talk to Sarah-Gene?”
“She the owner?”
“Nope. She’s just another volunteer.”
New volunteer job — 37-word long title
I’m thinking another fold-out business card may be required;
Volunteer
Vice Chair of Finance and Operations (of the)
Commercial and Business Users Constituency (which is part of the)
Generic Name Supporting Organization (which is in turn part of the)
Internet Corporation for Assigned Names and Numbers
Can you see why ICANN has a bafflegab problem?
I’m quite excited about this one — it’s got lots of tasty issues and it’s the ops and finance stuff that I love to do.
I had another fold-out business card job back in the early ’90’s. That fold-out business card read;
Temporary Interim Acting Assistant Associate
Vice President (supervising)
Administrative Information Systems
Business Operations
Quality Management
Operations Improvement (for the)
University of Minnesota
or… Vice President of Stuff that is Busted. This new gig is a lot less complicated than that one was.